A vast quantity of phishing emails get sent every day, trying to convince their recipients to click or open an attachment, some messages definitely stand out from the crowd.
Some of these are outstanding and very difficult to distinguish from legitimate emails. Some of them, on the other hand, are such failures that there is hardly any chance for them to be taken seriously. Since the aim of phishing is to get the sender to click on a link or open a file, some hackers are really less talented than the others.
As a part of our security awareness activities, we can't resist the urge to share some of the worst phishing emails we have received. We tried to guess what the author must be like.
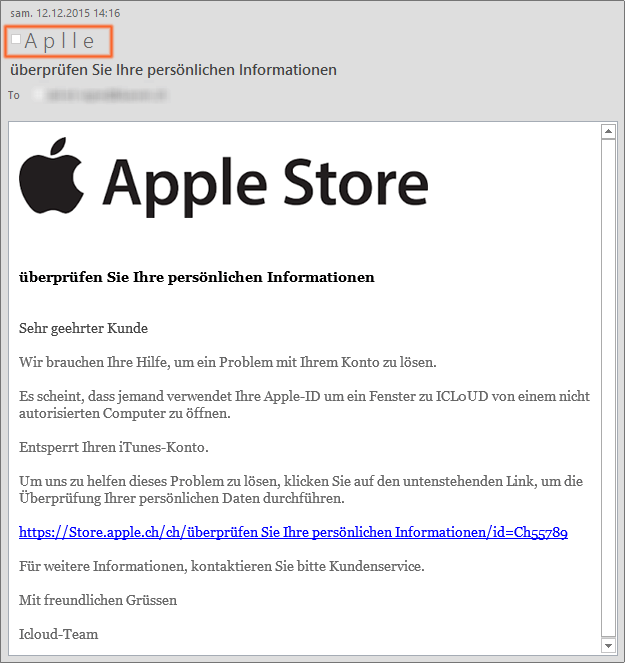
Absent-minded
When he created his sender's name, the hacker misspelt the word 'Apple'. Too bad.
Remiss
Spelling mistake again!...
Beginner
The content of the email was included in a picture. Unfortunately, the hacker forgot to check if the image was displaying correctly before he sent the message.
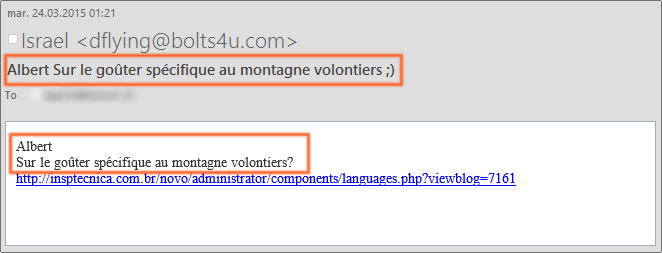
Puzzling
We still haven't understood the meaning of this mysterious message, nor the motivations of the sender. What was he looking for? What did he want? Are we in a parallel universe?
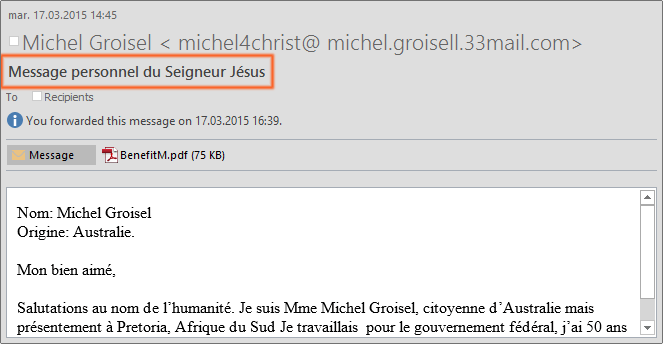
Ambitious
Wow, a message from Heaven!
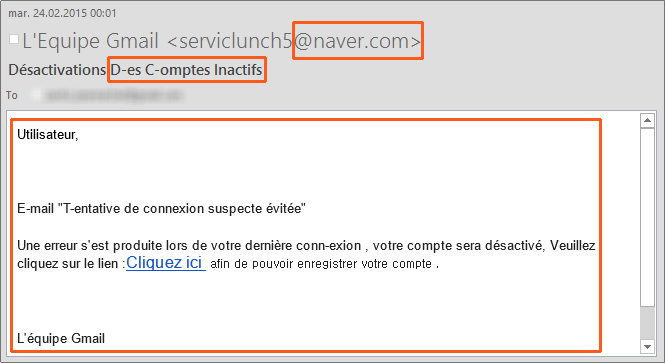
Beginner
This hacker did not even try to use a gmail address matching the supposed sender's name, even though it would have been easy to do so. He obviously also had S-ome L-a-Y-out problems. Beginner's nerves?
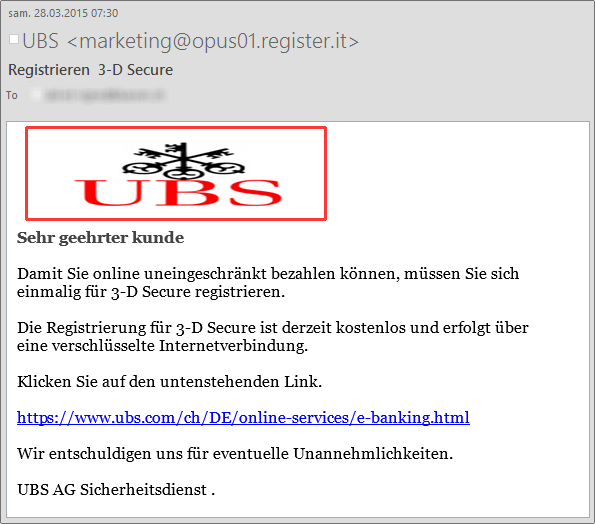
Careless
The sender wanted to make a good impression. Don't they say a picture is worth a thousand words? A logo is certainly good for credibility, isn't it?
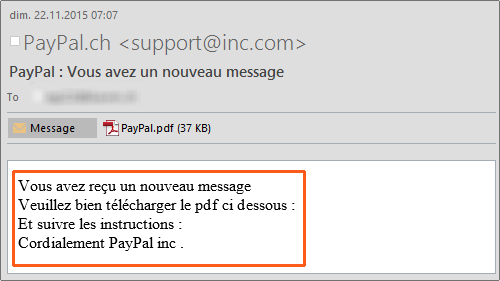
Teacher
This hacker prefers keeping the message clean and simple: four lines, four ideas. But he is betrayed by his email address. And, of course, the recipient of such a message would be well advised not to open the attached file, which is certainly contaminated.
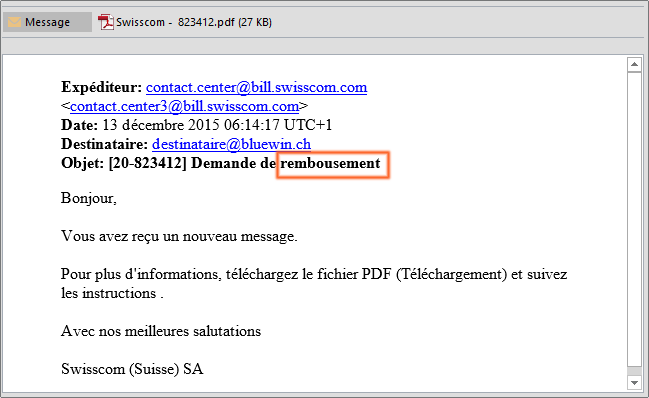
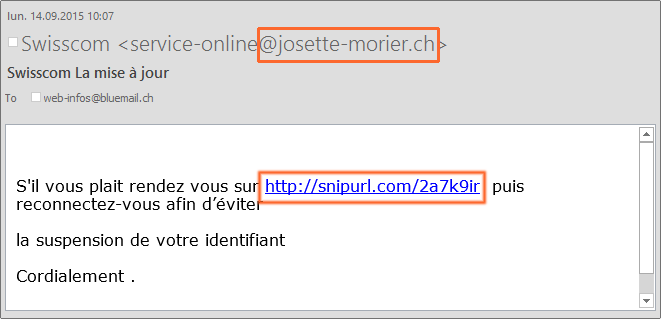
Optimistic
This hacker is totally uninhibited. Although he tries to pass as Swisscom, he does not bother to cover up his e-mail address or that of the clickable link, both of which have nothing in common with the Swiss operator.
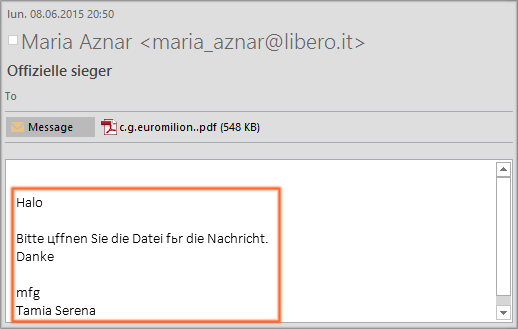
Cyrillic
Slav hackers sometimes have a hard time sending phishing emails, as Cyrillic fonts do not always convert smoothly to Western European encoding. This often betrays them.
Loud
'Get noticed', that's the hackers' motto! Spelling? Actual meaning? Who cares?
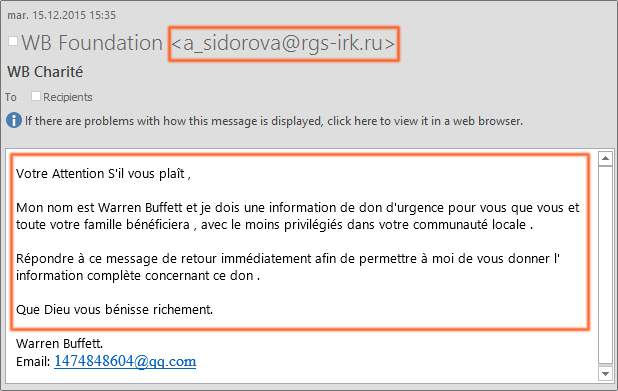
Benefactor
A message from the Warren Buffet Foundation, sent from a Russian email address? Why not? Better not use Google translate, though.
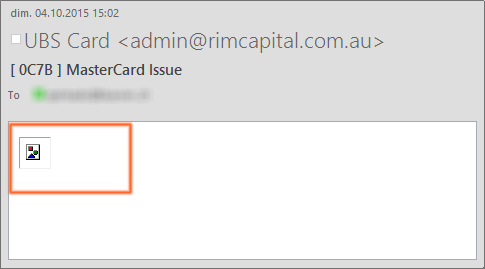
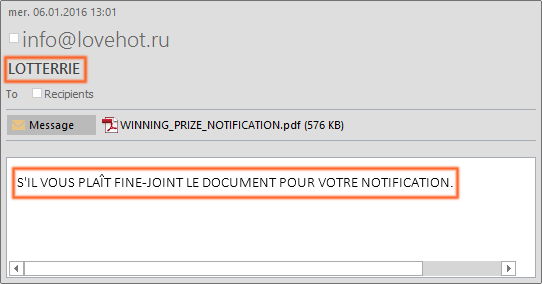
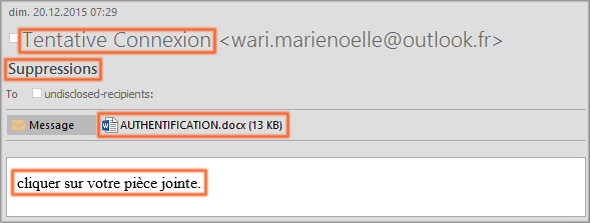
Minimalist
Nothing extra here, the hackers goes straight to the point. He wants the recipient to open the attachment, and his message is exactly five words long. There is however no relation between the sender, the message title and the name of the attachment.
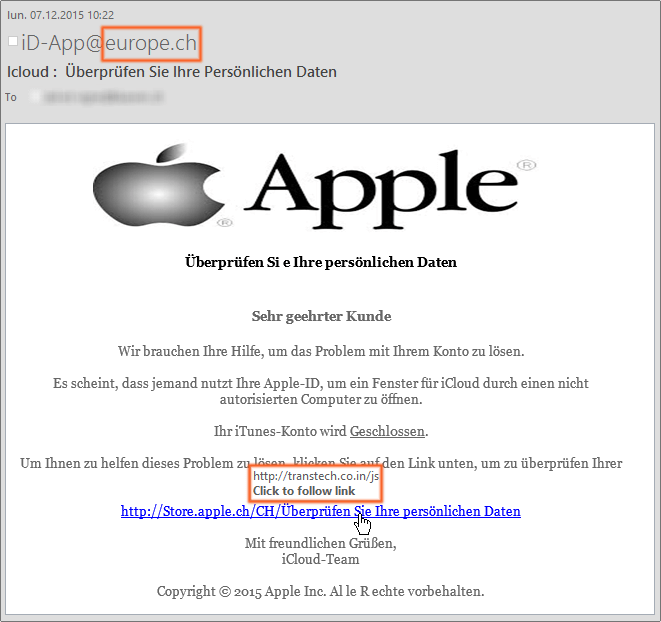
Brand addict
Again, the hacker seems to think that a logo will generate immediate trust. As a result, he does not even try to make the email look legitimate: the logo is distorted, and both the sender's email address and the clickable link are fanciful.
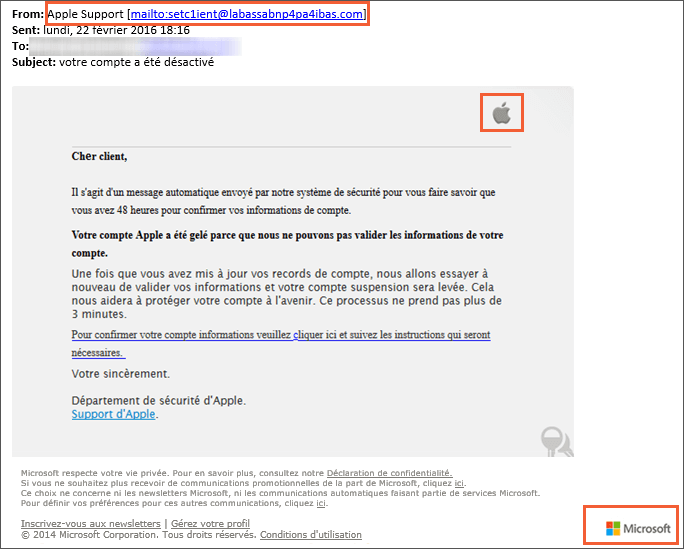
Utopist
The hacker wanted to cast a wide net and reach both Apple and Microsoft users in one single phishing email. Yeah, sure...